Trezor Login: Simplify and Secure Your Crypto Access
Take full control of your digital assets with Trezor login. Learn how to connect, authenticate, and safeguard your crypto portfolio with one of the most trusted hardware wallets in the world.
Understanding Trezor Login
The Trezor login process is your key to unlocking a secure world of crypto management. Instead of relying on passwords or cloud-based credentials, it uses physical verification through your Trezor device. This ensures that no one can access your funds without your direct authorization.
Trezor acts as your private digital vault, storing your keys offline. When you log in, you’re not entering data into a risky web form — you’re confirming identity directly on your hardware device.
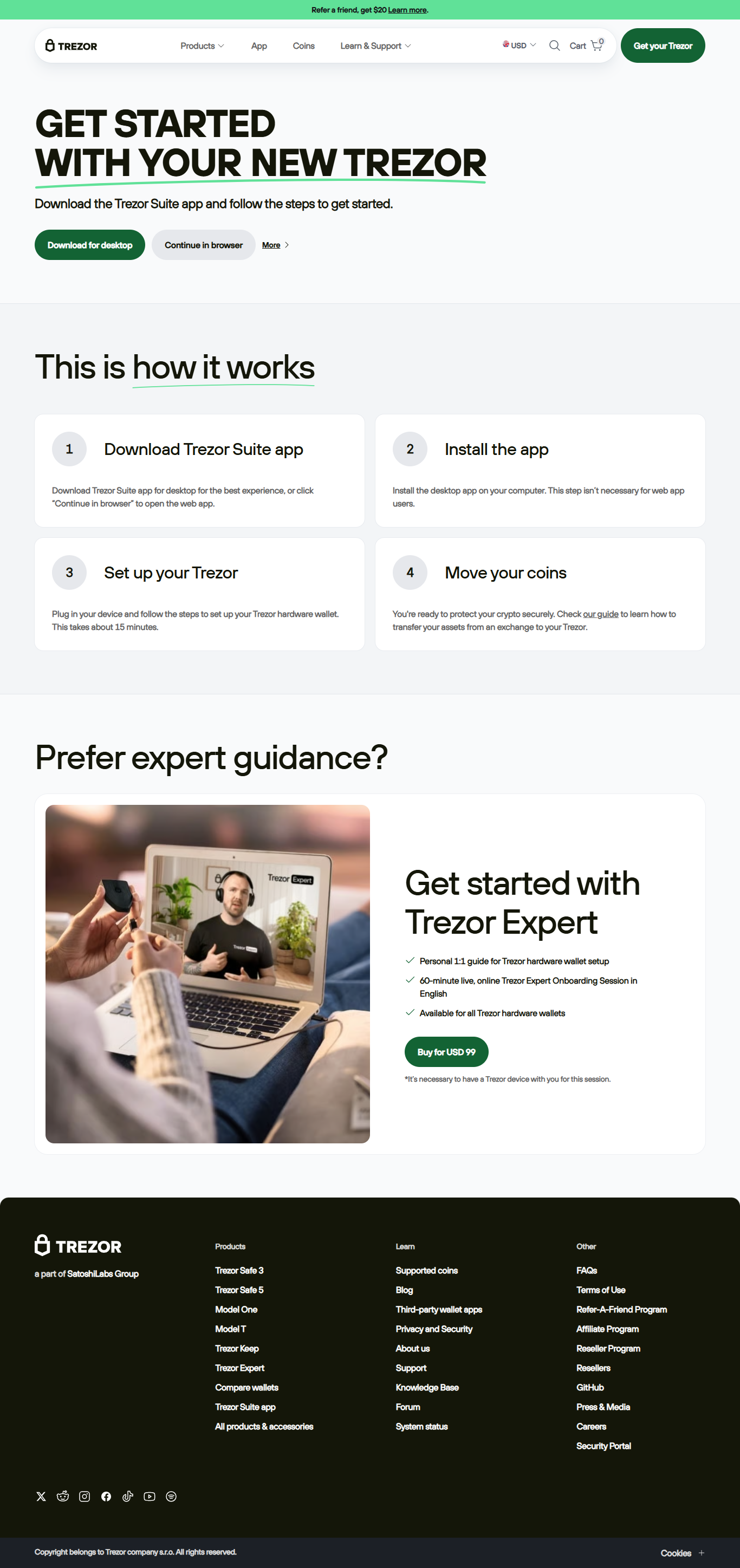
Step-by-Step Guide to Trezor Login
Here’s how you can easily log into your wallet while maintaining top-tier security:
Step 1: Go to the Official Site
Visit trezor.io — always ensure the URL and SSL certificate are authentic before proceeding.
Step 2: Plug in Your Device
Connect your Trezor via USB. The Trezor Bridge or Suite will automatically detect your device.
Step 3: Open Trezor Suite
Launch Trezor Suite, where you’ll manage assets, view balances, and confirm transactions.
Step 4: Confirm Login
Authenticate the login directly on your Trezor device. This physical confirmation prevents phishing or remote access attacks.
Why Trezor Login Outperforms Traditional Crypto Logins
- 🛡️ Hardware Security: All cryptographic operations occur within your Trezor chip.
- 🔏 No Password Vulnerability: No central server to be hacked or leaked.
- 🧭 Direct Ownership: Only you can approve transactions via your physical device.
- 🌐 Universal Compatibility: Works seamlessly with desktop apps and browsers.
Common Issues and Solutions for Trezor Login
1. Device Not Recognized
Ensure Trezor Bridge is installed. Try a different USB cable or port and restart your browser.
2. PIN Forgotten
Reset your device and recover using your 12/24-word recovery seed. Keep this seed offline and secure.
3. Login Page Not Loading
Update Trezor Suite or clear your cache. Use the latest Chrome or Firefox version for best performance.
Trezor Login vs Exchange Login
| Feature | Trezor Login | Exchange Login |
|---|---|---|
| Private Key Storage | Offline on hardware | Online on exchange servers |
| Authentication Type | Physical confirmation | Username/password |
| Risk of Hacks | Extremely low | High (server-based) |
| User Control | 100% user-owned | Custodial |
FAQ – Trezor Login Explained
1. Do I need my Trezor for every login?
Yes, your Trezor must be connected for authentication. This is the foundation of its hardware-level security.
2. What if I use multiple computers?
You can use your Trezor on multiple devices by installing Trezor Suite and Bridge on each one.
3. Can I log in without internet?
No, a basic internet connection is required to sync blockchain data, though all private key operations stay offline.
4. Is Trezor login free?
Yes, Trezor Suite and login features are completely free to use. You only need the hardware wallet.
Take Charge of Your Crypto Security
With Trezor login, you own your keys, your assets, and your financial freedom. Protect your digital wealth today with hardware-grade safety and unmatched simplicity.